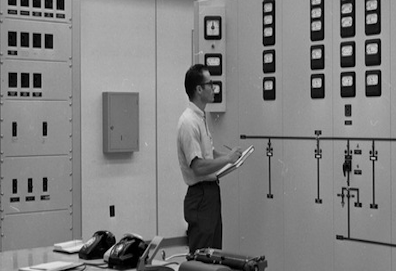
ICS Security Model
How would you view OT and control systems? Based on our research, the difference between OT and control systems are quite different.
How would you view OT and control systems? Based on our research, the difference between OT and control systems are quite different.

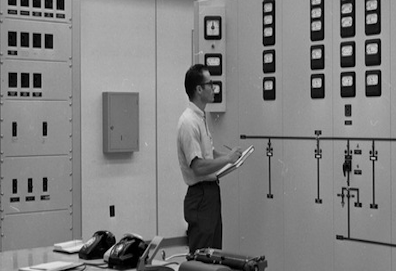
A deliciously easy way of defining how a strategic cybersecurity framework should be designed and implmented in any plant production.

A new definition that outlines what would happen if a cybersecurity event happened...that no one did anything to prevent it?